How Secure Coding Training fits within the PCI-DSS
The Payment Card Industry Data Security Standard (PCI DSS) is a proprietary information security standard for organizations that handle branded credit cards from the major card schemes including Visa, MasterCard, American Express, Discover, and JCB. The PCI Standard is mandated by the card brands and administered by the Payment Card Industry Security Standards Council. The standard was created to increase controls around cardholder data to reduce credit card fraud. Validation of compliance is performed annually, either by an external Qualified Security Assessor (QSA) or by a firm specific Internal Security Assessor (ISA) that creates a Report on Compliance (ROC) for organizations handling large volumes of transactions, or by Self-Assessment Questionnaire (SAQ) for companies handling smaller volumes.
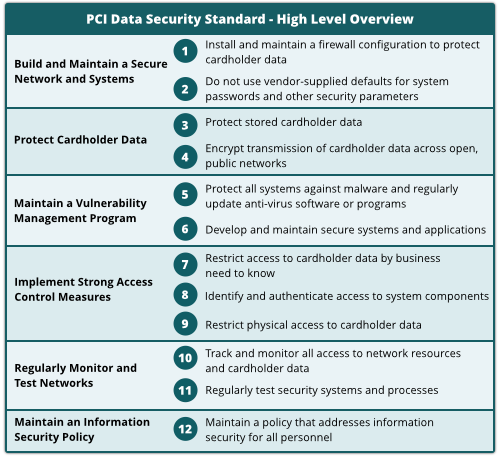
I was approached a while back by a company based in Europe, who wanted a comprehensive training for their software engineers. After discussing with my contact, it became clear they needed secure coding education in order to achieve PCI-DSS accreditation. Let us have a look at the high-level overview of what PCI-DSS is really about :
As you can see, PCI-DSS is broken down in different sections. Each one of those covering a specific subject. Within the “Maintain a Vulnerability Management Program” part, section 6 states : “Develop and maintain secure systems and applications”.
That right there is exactly where secure coding education fits.
When talking about secure applications, more othen than not people think about threat modelling… Pentesters… Ethical hacking etc. As much as all of those are necessary nowadays, they still tackle the problems AFTER the code is “born”. With secure coding education, you will actually ensure that the code produced is already of high quality, contains less bugs and is then easier to look at, and fix.
Not only will you get better code quality, but you will also get better employees straight after the training is delivered, better performances both from your developers and security specialists (Better code will have an impact on how you can use your #infosec specialists).
Web Application Compliance
Since most found vulnerabilities come from Web Applications, PCI-DSS addresses those in section 6.6 (organizations are to ensure the highest level of application security).
Most companies make use of two different tactics in order to achieve that. The first one is a yearly code review, the second one is to use firewalls.
The problem with firewalls is that you will not detect (and then… not fix) vulnerabilities. Instead it will protect you against them. We do not recommend using that one.
Code review is what most companies aim for. It is recurrent, more expensive… but has better results. The “find, fix and text” process does not always find all vulnerabilities in the code, and then needs to be repeated for several cycles. Zero-day vulnerabilities are also to be kept in mind. Most companies will have a structure in place that should follow this pattern (whether in-house or outsourced) :
- Services by application security specialists
- IT resources to manage the code review process
- Development resources for eliminating vulnerabilities
- QA resources
- R&D risks entailed by development of security fixes and feature
But do you want to know what the BEST companies do?
The BEST companies TRAIN their workforce !
Educate your Engineers on Secure Coding Best Practices
As mentioned earlier, we have just finished training up a client’s entire engineering department on secure coding best practices to help them on their path to PCI-DSS certification. Our calendar for august and September is full, we are however still available for some training sessions during October and November.
Curious to find out what is behind this picture? Get in touch to find out!
And don’t forget… The best companies use the MOST training!